✨ The Containment Era is here. Secure AI workloads before they breach. →The Containment Era is here. →The Containment Era is here. →Explore ✨
F500 Financial Institution Case Study
F500 Financial Institution Case Study, direct customer interview conducted by Industry Analyst firm Enterprise Management Associates (EMA). Highlights Aviatrix Secure Cloud Networking and Distributed Cloud Firewall.
Keep exploring
Related Resources

Global Animal Health Leader Closes Cloud Security Gaps and Unifies Multicloud Networking with Aviatrix Cloud Native Security Fabric
Learn how a global animal health technology leader overcame multicloud security and complexity with Aviatrix Cloud Native Security Fabric.

Securing AI Agents Across Clouds
Agentic AI can transform how your business operates — but autonomous, multi-agent workflows running across clouds introduce security risks that traditional tools were never designed to handle. Data exfiltration, cascading workflow failures, and uncontrolled lateral movement are all real threats when AI agents operate with minimal human oversight. This case study shows how Aviatrix Cloud Native Security Fabric (CNSF) provides the security foundation that agentic AI actually requires.
The Containment Era — Why the Threat Model Outgrew the Architecture
The Cascade attack of March 2026 proved what security leaders suspected: detection-first architecture can no longer keep pace with threats that move through trusted channels. This whitepaper examines the Architectural Divide, the growing gap between cloud workload deployment and security enforcement, and explains why blast radius has become the metric that matters most. Download to understand the structural shift your security strategy needs to address.
Architecture Won - A Fortune Global 500 Enterprise Has the Block Logs to Prove It
A Fortune Global 500 enterprise used Aviatrix to quickly block malicious IPs tied to the LiteLLM supply chain attack. The casestudy highlights how the right cloud security architecture enables fast action, real-time enforcement, and stronger protection without added complexity.
The Financial Services Architectural Divide: Securing Digital Assets and Regulatory Trust at Fintech Speed
Financial institutions have scaled their cloud infrastructures to meet the demands of a 24

Global Biopharmaceutical Leader Accelerates R&D from Months to Hours with Cloud Native Security Fabric
Learn how a global biopharmaceutical leader who needed guaranteed multicloud security, resiliency, and performance discovered Aviatrix Cloud Native Security Fabric (CNSF). CNSF empowered this organization to:
Aviatrix Breach Lock: Rapid Response Program for Cloud Data Exfiltration
When attackers gain a foothold in your cloud environment, data exfiltration can begin within seconds. Long before your DFIR team has established situational awareness, sensitive data is already moving. CNAPPs surface posture issues. EDR protects endpoints. SASE secures the perimeter. None of them stop workload-driven cloud egress during an active incident. Aviatrix Breach Lock is a free rapid response program that gives organizations immediate visibility, workload-level attribution, and cloud native egress containment during an active or suspected breach, with no agents, no downtime, and no architecture changes.

Navigating Cloud Network Security While Prioritizing Scale and Compliance
Financial services organizations are running multicloud environments to power innovation, meet customer expectations, and stay ahead of regulatory change. But that same complexity creates an unprecedented volume of data in motion, and the perimeter-based security models most institutions still rely on were never built for it. This ebook is a practical guide for financial services security and cloud leaders who need to scale cloud adoption without compromising compliance, resilience, or control.
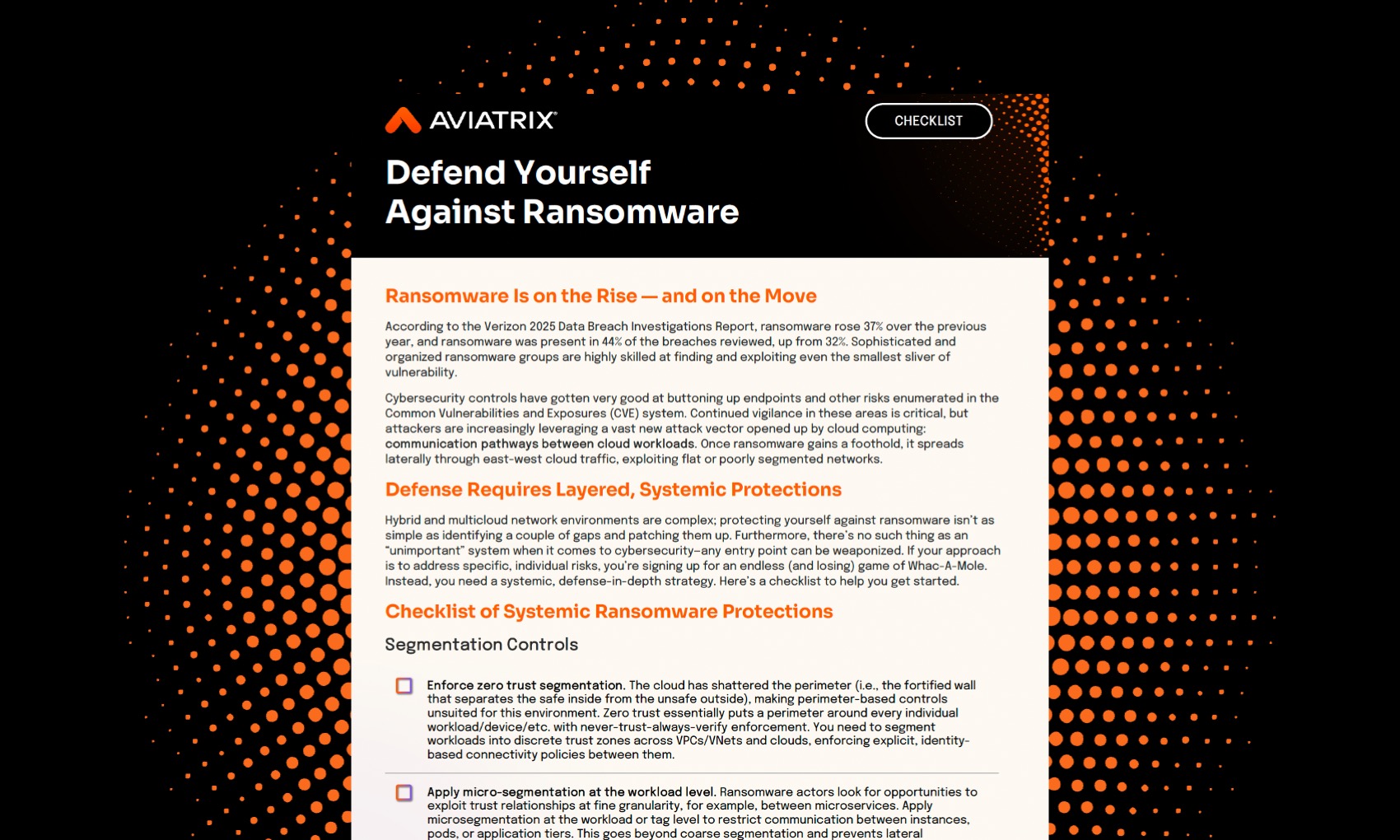
Defend Yourself Against Ransomware: Checklist
Hybrid and multicloud network environments are complex; protecting yourself against ransomware isn’t as simple as identifying a couple of gaps and patching them up. You need a systemic, defense-in-depth strategy to blanket your environment with protection against ransomware. This checklist helps you get started, with real-world guidance including enforcing zero trust segmentation, centralizing policy management and visibility, and implementing always-on risk scoring.
Ready to Transform your Cloud Network Security?
Manage, simplify, and secure your infrastructure across cloud providers with Aviatrix.

