✨ 2026 Futuriom 50: Key Findings and Highlights →2026 Futuriom 50: Highlights →2026 Futuriom 50: Highlights →Explore ✨
Five Zero Trust Blind Spots That Put Your Cloud At Risk
You've implemented zero trust for users but that's just the beginning. Aviatrix delivers the visibility, encryption, segmentation, and automation needed for a complete zero trust strategy.

Keep exploring
Related Resources

Global Biopharmaceutical Leader Accelerates R&D from Months to Hours with Cloud Native Security Fabric
Learn how a global biopharmaceutical leader who needed guaranteed multicloud security, resiliency, and performance discovered Aviatrix Cloud Native Security Fabric (CNSF). CNSF empowered this organization to:
Stop Lateral Movement: Runtime Zero Trust Containment for Cloud Workloads
Cloud breaches rarely cause serious damage at the point of entry. The damage happens after, when attackers move laterally across workloads using valid credentials and trusted network paths that no one is governing. IAM stops unauthorized access. EDR and SIEM detect suspicious activity. But none of them stop movement once an attacker is already inside. This solution brief explains how Aviatrix
Block Data Exfiltration: Runtime Zero Trust Control for Outbound Cloud Communication
Data breaches don't cause damage at the moment of entry. They cause damage when sensitive data leaves, quietly, over encrypted outbound connections that look completely legitimate. DLP tools need to inspect payloads. SIEM and EDR alert after the data is already gone. Perimeter firewalls were never designed to govern distributed cloud egress. Aviatrix takes a different approach entirely: instead of inspecting what the data is, it controls where the data can go, enforcing Zero Trust on outbound cloud communication before anything leaves the environment.

Accelerate Secure Developer Velocity: Enable Fast Cloud Delivery with Runtime Zero Trust Guardrails
Cloud native development moves fast. Security controls often don't. Most organizations slow delivery by inserting reviews, approvals, and manual gates into CI/CD pipelines. Developers wait on tickets. Firewall changes delay releases. Temporary exceptions become permanent risk. The problem is not a lack of security tooling. It's where and when security is enforced. This solution brief explains how Aviatrix shifts security from a deployment gate to an always-on guardrail, so developers can move fast without increasing risk and security maintains continuous control without slowing anyone down.
Aviatrix Breach Lock: Program Brief
In this program brief, learn about how Aviatrix Breach Lock works, including key program benefits like immediate exfiltration containment, visibility behind NAT, cloud native, agentless enforcement, and multicloud enforcement.
Aviatrix Breach Lock: Rapid Response Program for Cloud Data Exfiltration
When attackers gain a foothold in your cloud environment, data exfiltration can begin within seconds. Long before your DFIR team has established situational awareness, sensitive data is already moving. CNAPPs surface posture issues. EDR protects endpoints. SASE secures the perimeter. None of them stop workload-driven cloud egress during an active incident. Aviatrix Breach Lock is a free rapid response program that gives organizations immediate visibility, workload-level attribution, and cloud native egress containment during an active or suspected breach, with no agents, no downtime, and no architecture changes.

Stop Advanced Threats (APTs & Ransomware)
APTs and ransomware campaigns rarely succeed because of a perimeter failure. They succeed after initial compromise, when attackers move laterally between workloads, establish command-and-control, and exfiltrate data through trusted cloud paths that no one is governing at runtime. SIEM, EDR, and CNAPP tools surface alerts. They do not stop movement. This solution brief explains how Aviatrix Cloud Native Security Fabric enforces Zero Trust directly inside cloud and hybrid workload communication paths, limiting attacker movement before ransomware spreads and before data leaves the environment.
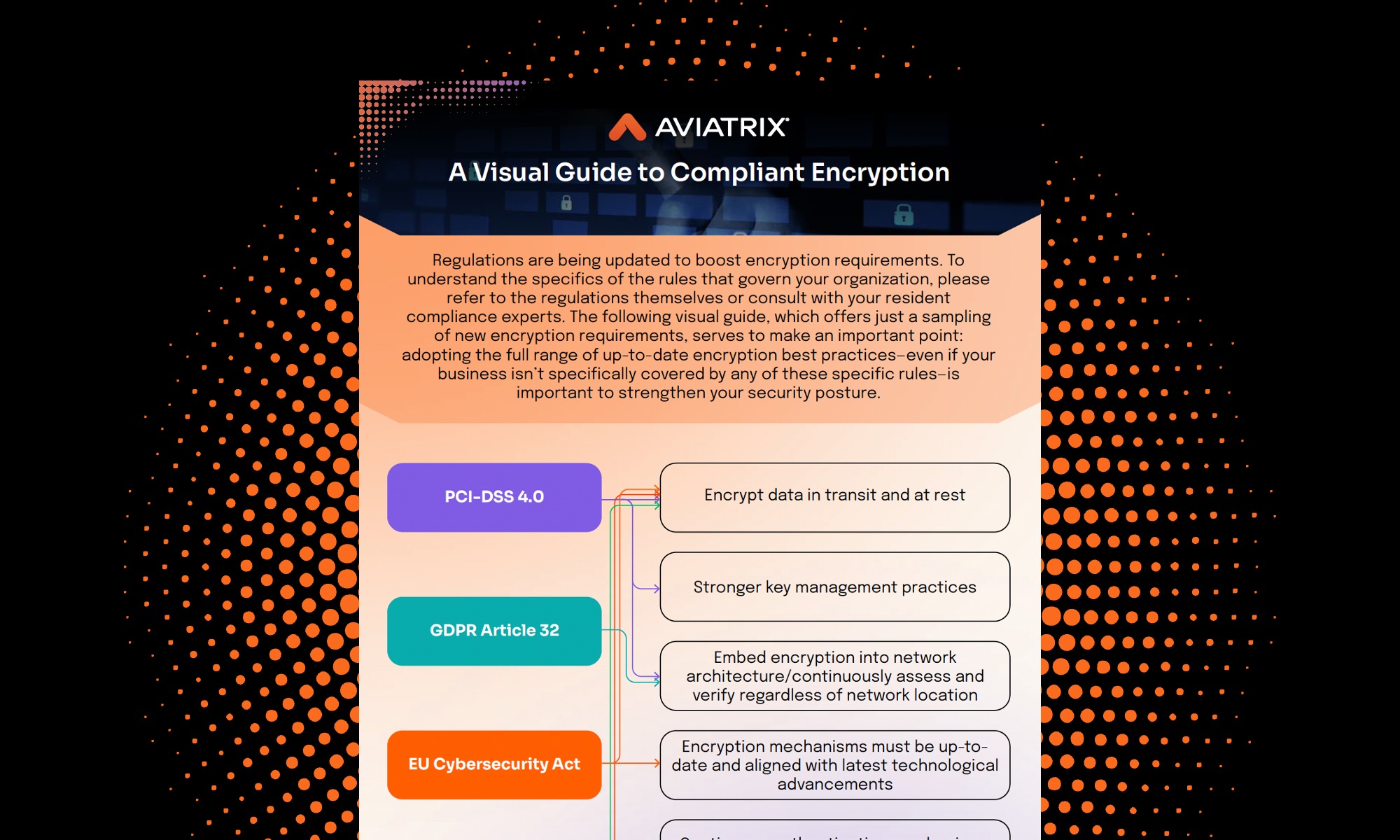
A Visual Guide to Compliant Encryption
Regulations are being updated to boost encryption requirements -- are you staying up to date? The following visual guide offers just a sampling of new encryption requirements. Adopting the full range of up-to-date encryption best practices—even if your business isn’t specifically covered by any of these specific rules—is important to strengthen your security posture.
Aviatrix Workload Attack Path Assessment
Assess risks with confidence with the Aviatrix Workload Attack Path Assessment a free, agentless assessment that reveals how real attacks could move through your cloud.
Ready to Transform your Cloud Network Security?
Manage, simplify, and secure your infrastructure across cloud providers with Aviatrix.

