✨ The Containment Era is here. Secure AI workloads before they breach. →The Containment Era is here. →The Containment Era is here. →Explore ✨
The Containment Platform for Every Cloud Workload
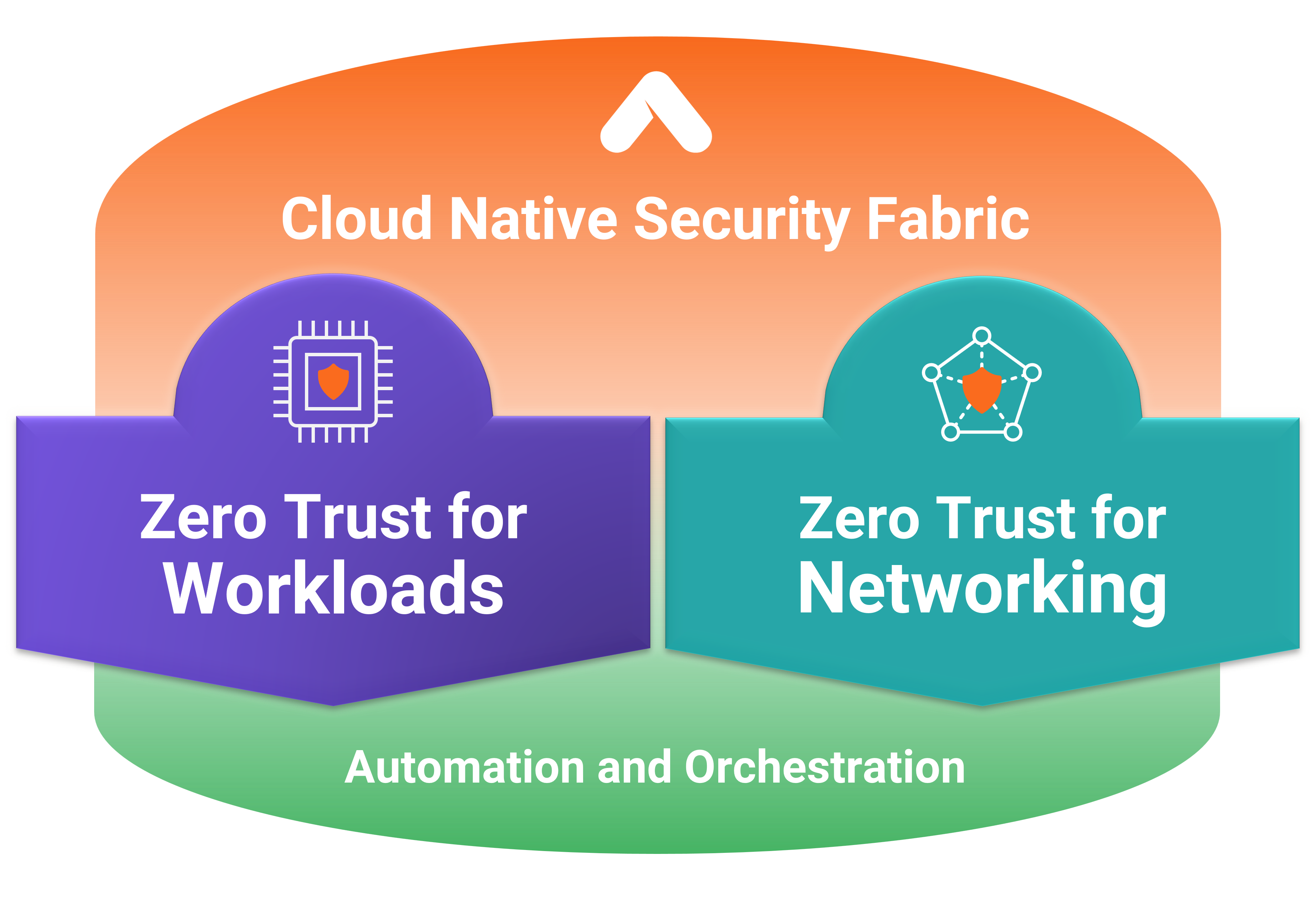
Realize NIST & CISA's Zero Trust goals. CNSF is the embedded enforcement fabric that makes Zero Trust a reality.
When prevention fails and detection is too slow, containment decides whether the incident becomes a breach.
Chokepoint Security vs. Containment Architecture
A chokepoint governs the traffic that routes through it. Communication Governance governs every path.
Transit
Firewall
Detailed Comparison
"The distinction is not 'egress filtering vs. no egress filtering.' The distinction is where the enforcement lives."

Inside Real Breaches: How CNSF Stops Lateral Movement and Data Theft
Learn from MGM Resorts and MOVEit: attackers used social engineering and supply chain exploits to move east-west and steal data. The whitepaper shows how Cloud Native Security Fabric blocks lateral movement, contains blast radius, and stops unintentional data leakage.
Containment, Built Into the Fabric
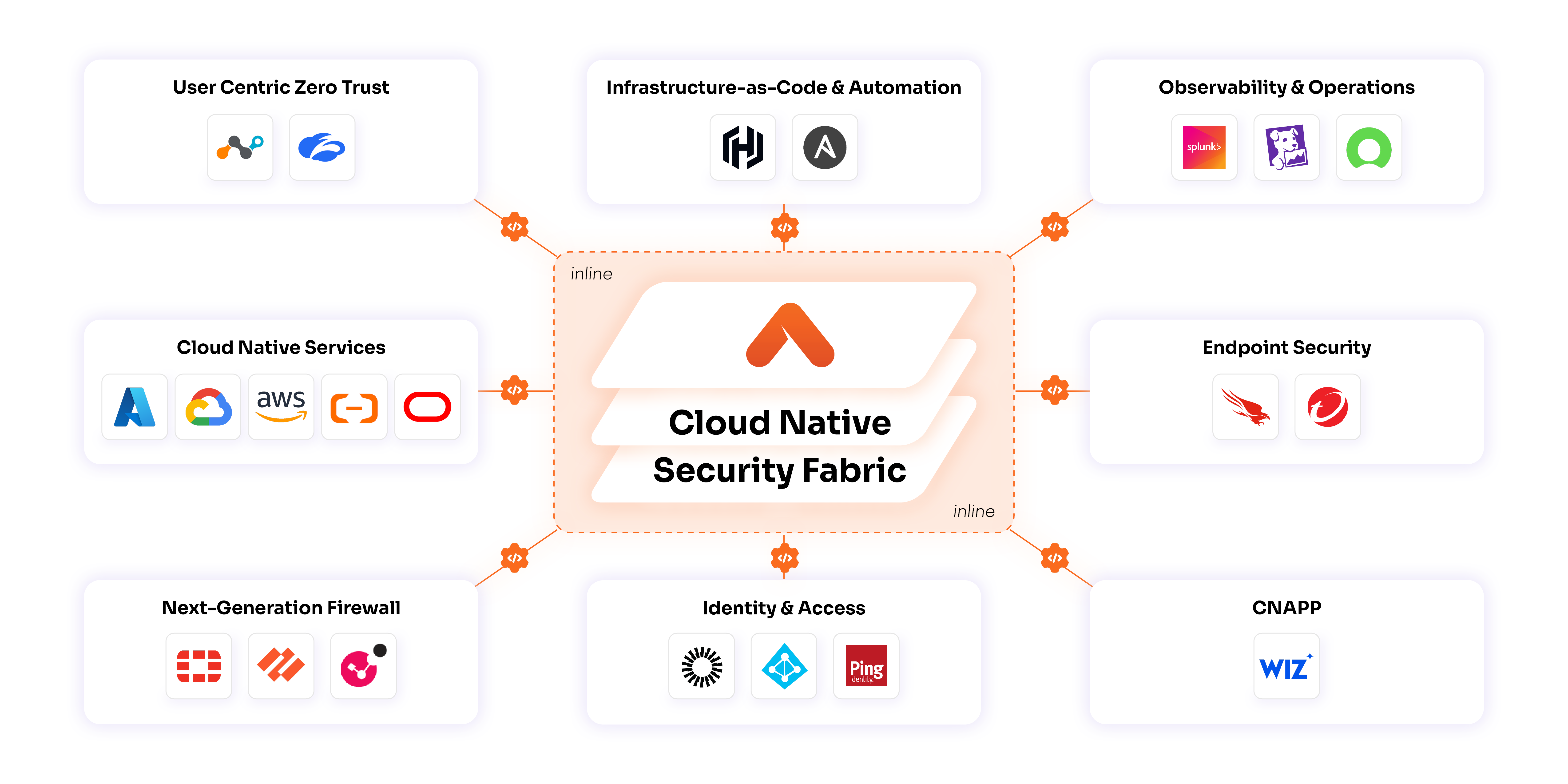
Instead of bolting security onto the edge, Aviatrix Cloud Native Security Fabric™(CNSF) weaves runtime enforcement into the cloud fabric. In-line points broker least-privilege connections, while one control plane applies consistent policy everywhere.
- AVIATRIX CLOUD NATIVE SECURITY FABRIC (CNSF)
Here’s How CNSF Changes Cloud Security:
Policies live inside your cloud—not the edge.
Segmentation moves with workloads automatically.
No agents, no middleboxes, no bottlenecks.
Every session verified instantly, with no lag.
Unified protection across multicloud, on-prem, edge, containers, functions and AI workloads with consistent security.
Developer-friendly. Operates below the app layer—no code changes or DevOps friction.
Strong controls with negligible latency.

Zero Trust for Workloads
Aviatrix Zero Trust for Workloads secures workload-to-workload and workload-to-internet traffic in real time. Deployed within existing cloud architectures, it does not require network redesign.


Zero Trust for Networking
Aviatrix Zero Trust for Networking, built on High-Performance Encryption (HPE) secures the fabric itself—ensuring that every connection is encrypted, auditable, and performance-optimized.


Minimize Your Cloud Breach Risk
CNSF is the missing "how" for Zero Trust, delivering the implementation for NIST & CISA goals . As an in-line enforcement fabric, it provides measurable outcomes: fewer breaches, consistent policy, and simpler compliance.


Reduce Cloud Attack Surface
Hide apps behind identity-based policies. Workloads are isolated and invisible by default, shrinking exposure.
Stop Live Attacks
CNSF is in-line, not just a scanner. It contains threats by default, minimizing the blast radius.
Prevent Data Exfiltration & Prove Compliance
Default end-to-end encryption secures all in-transit data per CISA mandates. Unified audit trails and policy abstraction simplify compliance across AWS, Azure, and GCP.
Gain Measurable Outcomes
Track reduced dwell times and breach risks with centralized visibility. Embed Zero Trust for K8s, serverless, and AI—accelerate innovation while proving ROI to CISOs.
500+ Enterprises Secure Cloud and AI with Aviatrix
Including 10% of the Fortune 500



















Cloud Security Insights & Best Practices
See Aviatrix CNSF in action.
Request a demo and discover how CNSF secures your cloud end-to-end. Explore use cases, assess your posture, and eliminate blind spots while accelerating initiatives.