TL;DR
AI agents represent significant challenges for CISOs and other security leaders: they behave differently, reason differently, and operate by rules that can evade traditional security tools and policies.
Traditional security solutions such as endpoint security or CNAPP are not equipped to handle the risks of AI agents, even when layered and use to complement each other.
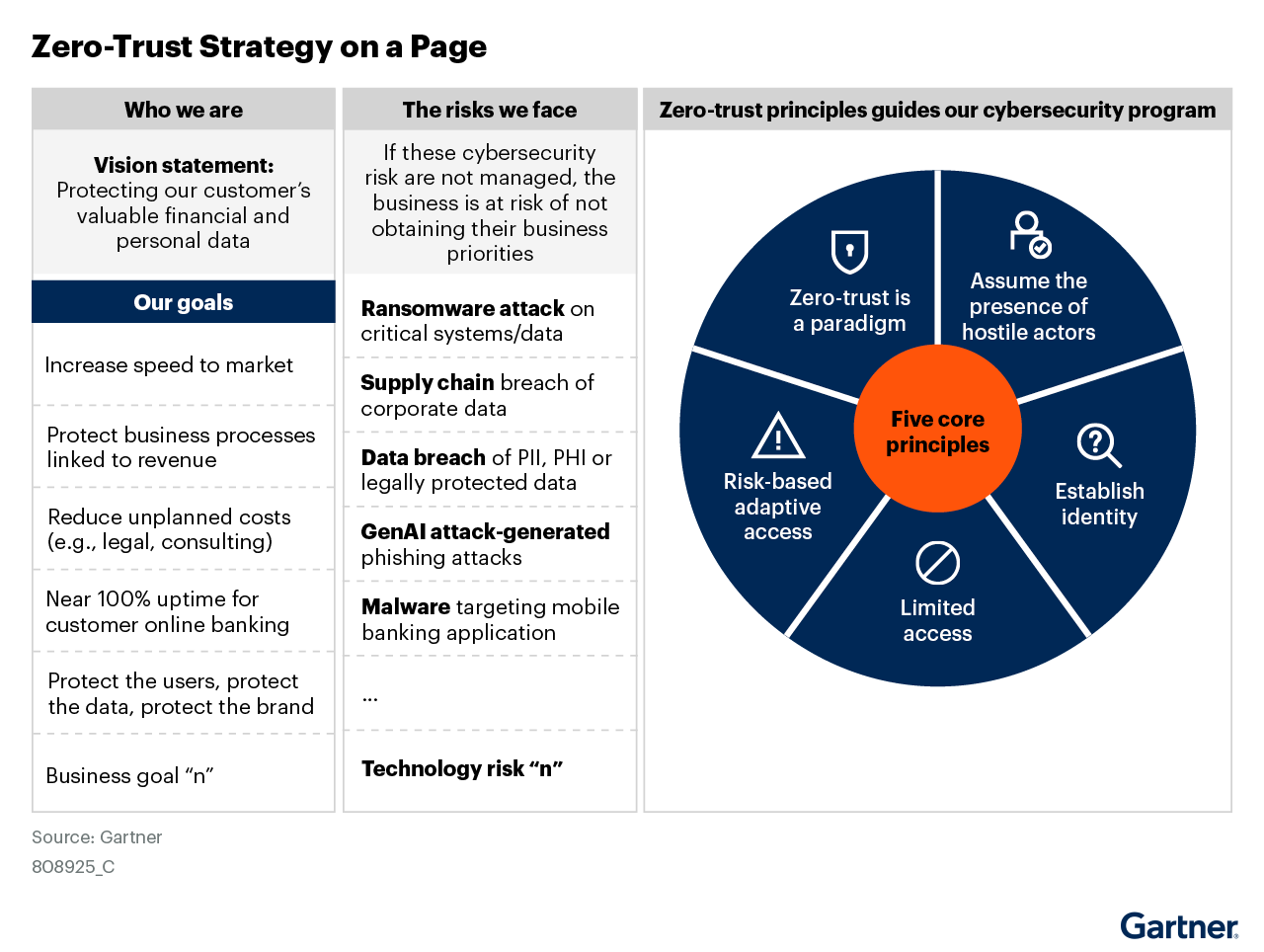
Organizations need a cloud native, workload-centric, Zero Trust security solution to secure AI agents for future innovation.
Security incidents that involve AI agents make headlines at least once a week. This year, we've had a Cascade of them:
Trust chain attacks by groups like TeamPCP, North Korea’s UNC, LAPSUS$, and more that harvested credentials from cloud environments
The Claude data exfiltration vulnerability that chained together multiple weaknesses to steal user chat data
The OpenClaw agent that creates a high-risk vector for lateral movement across your network at machine speed.
The scope and breadth of these attacks show that we need to rethink our paradigm for security. We’ve left behind the Detection Era in which security leaders tried to keep attackers out of networks into the Containment Era, where we shift to focusing on communication governance to stop data exfiltration. Shifting into the Containment Era is even more important in the subcategory of agentic AI security because AI agents can gain unprecedented access to data and systems.
As CISO of Aviatrix, I am deeply invested in securing AI agents to maximize innovation safely. I created a case study of how our organization and solution, Aviatrix Cloud Native Security Fabric (CNSF), secure AI agents at the network layer to stop lateral movement, block data exfiltration, and accelerate secure developer velocity so that we can maximize our AI use safely.
Why AI Agents Present Unprecedented Security Risks
In the case study, I cover the reasons why AI agents pose network security risks, including:
Autonomous decision-making and tool usage – While traditional solutions follow logical, step-by-step workflows, AI agents are tasked with executing commands given in natural language. Their very nature makes them non-deterministic and unpredictable, making them nearly impossible for traditional security tools to manage.
Delegation and multi-agent collaboration – Multiple agents can work together to complete a task, creating a chain of commands, reasoning, and actions that can break security policies without detection.
Agent identity vs. user identity – Traditional security policies are set based on identity: resources are gated so that only authorized users can access them. AI agents automatically gain the permissions of the user who commissioned them and may become shared or abstracted, making it difficult to enforce those security policies.
These and other characteristics of AI agents make visibility, policy violations, and risks difficult to manage for security teams.
The Limits of Traditional or Chokepoint Security
Security tools such as Identity and Access management, endpoint protection, application layer controls, and cloud provider default security are not sufficient to enforce policies for autonomous and ephemeral AI workloads with broad permissions. The case study examines each layer of the security stack and why a new security paradigm is necessary.
Aviatrix CNSF: Protection at the Network Layer
The case study explains how Aviatrix CNSF mitigates these security risks by enforcing security policies at the network layer. CNSF operationalizes Zero Trust principles such as communication governance and least-privilege access with features like:
SmartGroups for Workloads – Aviatrix SmartGroups can categorize resources based on IP addresses or identity attributes such as namespaces or cloud tags, enabling security teams to create and enforce policies that apply to ephemeral AI agents.
Secure multicloud fabric – Aviatrix gateways form a private overlay network across multi-cloud where agentic workloads and communication between them never have to be exposed to the public internet.
Unified Observability – Aviatrix CNSF provides detailed audit logs of all traffic streams, empowering security teams to spot shadow AI or unauthorized use.
The chokepoint security of previous era’s perimeter-based models cannot prevent the kind of data exposure and network damage that misused AI agents can cause. Worse, they may give an illusion of security or waste security teams’ time as they try to enforce security policies through solutions never designed to handle the unpredictable behavior, reasoning, and ephemeral nature of AI workloads.
Aviatrix CNSF offers a security solution that matches the paradigm shift presented by agentic AI: a unified fabric that empowers security teams to enable agentic AI innovation safely across clouds, environments, and locations. As we move into the Containment Era of threat response where we focus on what workloads can reach vs. keeping the bad guys out, CNSF becomes the critical enforcement layer to ensure secure AI innovation.
Read the full case study, Securing AI Agents Across Clouds: A Reference Architecture.
Learn more about how the trust chain attacks of early 2026 show the shift from a Detection Era of cloud security to the Containment Era.
Frequently Asked Questions
AI agents do not follow fixed steps. They reason, plan, and act on their own, calling tools and other agents without human approval. They run in short-lived containers, share credentials, and spread across many clouds. Because their actions come from a model's decisions rather than written code, old rules about "who can do what" break down fast. This makes it hard to predict what an agent will do next, and harder still to stop it from doing harm.
Chokepoint security watches traffic at the edges of a network, like a front gate. But most agent-to-agent and agent-to-tool traffic moves inside the network, never reaching that gate. Firewalls work on IP addresses, which break down when agents spin up and disappear in seconds. Web application firewalls check for bad syntax, but agent messages are valid JSON even when they carry harmful instructions. Each cloud also has its own rules, so there is no single shared view of what agents are doing.
Aviatrix CNSF groups agents and tools by their role and cloud tags, not by fixed IP addresses. It then applies strict "allow only what is needed" rules between those groups. This communication governance means a support agent can reach its allowed tools but is blocked from reaching unrelated data stores or outside endpoints. Even if an agent is tricked into sending data to an attacker's server, the network layer drops the request before it leaves.
Prompt injection happens when a bad actor hides harmful instructions inside data that an agent reads, like a support ticket. The agent follows those instructions as if they were real tasks. Since the agent holds valid access keys, identity systems and web filters see nothing wrong. Without network-layer controls, the agent can pull sensitive data and send it out. Communication governance at the network layer blocks that outbound path even when other defenses miss it.
Agents often live for only seconds or minutes, leaving no lasting footprint for endpoint tools to capture. Aviatrix CNSF logs every traffic flow across all clouds in one place, giving security teams a full audit trail even after a workload is gone. This same visibility helps teams spot shadow AI, meaning agents or tools deployed outside approved channels, by flagging unexpected calls to AI endpoints. All logs can be sent to tools like Splunk for long-term storage and review.