TL;DR
Zero Trust principles are becoming increasingly necessary in the cloud as threat actors use AI and other advanced techniques to accelerate attacks.
Gartner® Strategic Roadmap for Zero-Trust Security Program Implementation makes Zero Trust possible for enterprises by outlining practical steps for setting a plan, creating a team, and measuring progress.
Zero Trust Network Architecture (ZTNA) has become a staple in cloud security since John Kindervag introduced the concept in 2009, but it is still more of a dream than a reality or even a plan for many enterprises. Our State of Cloud Network Security: 2025 report found that only 8% of surveyed enterprises used ZTNA. Many are stuck with the old implicit trust model of legacy, perimeter-based security models or with dangerously incomplete Zero Trust implementations.
With cyberattacks increasing in frequency and speed, implementing Zero Trust is more urgent than ever. CrowdStrike’s 2026 Global Threat Report found that the average eCrime breakout time dropped to 27 seconds, and attacks by AI-enabled adversaries increased by 89% in 2025.
The Gartner report empowers organizations to operationalize Zero Trust. It explains what pitfalls cause failed Zero Trust initiatives and how enterprises can set a vision, gather the right stakeholders, and create a coherent plan to move from implicit trust to a robust Zero Trust model
What is Zero Trust, and Why is it Important?
The report defines Zero Trust as “a security model that eliminates implicit trust, instead focusing on the continuous evaluation of explicit access and trust levels. This evaluation is based on identity and context, with a security infrastructure that adapts to optimize the organization’s security posture against specific risks.” It protects corporate data, property, and brands by instituting security controls that make it more difficult for threat actors to move laterally within networks, steal data, take over accounts, or inflict damage such as malware.
Zero Trust adoption is lagging, and not just because enterprises haven’t tried it. Many have tried and failed: “Gartner observed in the 2024 State of Zero Trust Adoption Survey that around 63% of respondents had either attempted or partially attempted a zero-trust initiative, with about 35% reporting failures in their initiatives that adversely affected their organization.”
What are Some Practical Steps to begin Zero Trust Implementation?
The Gartner report outlines practical steps for executives, security leaders, engineering leaders, and other stakeholders to begin with Zero Trust, including:
Asking your why – Establish why your organization needs a Zero Trust approach and what that means for you. This why may look different based on your organization’s size, industry, structure, culture, and other distinctives.
Setting goals – Set specific goals for infrastructure, policies, teams, and timelines to avoid a stalled or failed Zero Trust implementation.
Examining current state vs. future state – Compare the current state of your security policies, enforcement, visibility, and authentication to the goals you’ve set – and then, decide where the gap is and how to begin.
Determining your “risk appetite” and mitigation strategies – Determine the risks at play, what risks your organization wants to take, and how to mitigate them. An overly aggressive Zero Trust implementation could threaten productivity and long-term success, while a slow one could become a security threat or lose momentum.
Narrowing your scope – Instead of launching an overwhelming number of Zero Trust vendor solutions and complex policies, narrow your scope to focus on your most important assets and most critical weaknesses.
How Can an Enterprise Create a Zero Trust Strategy?
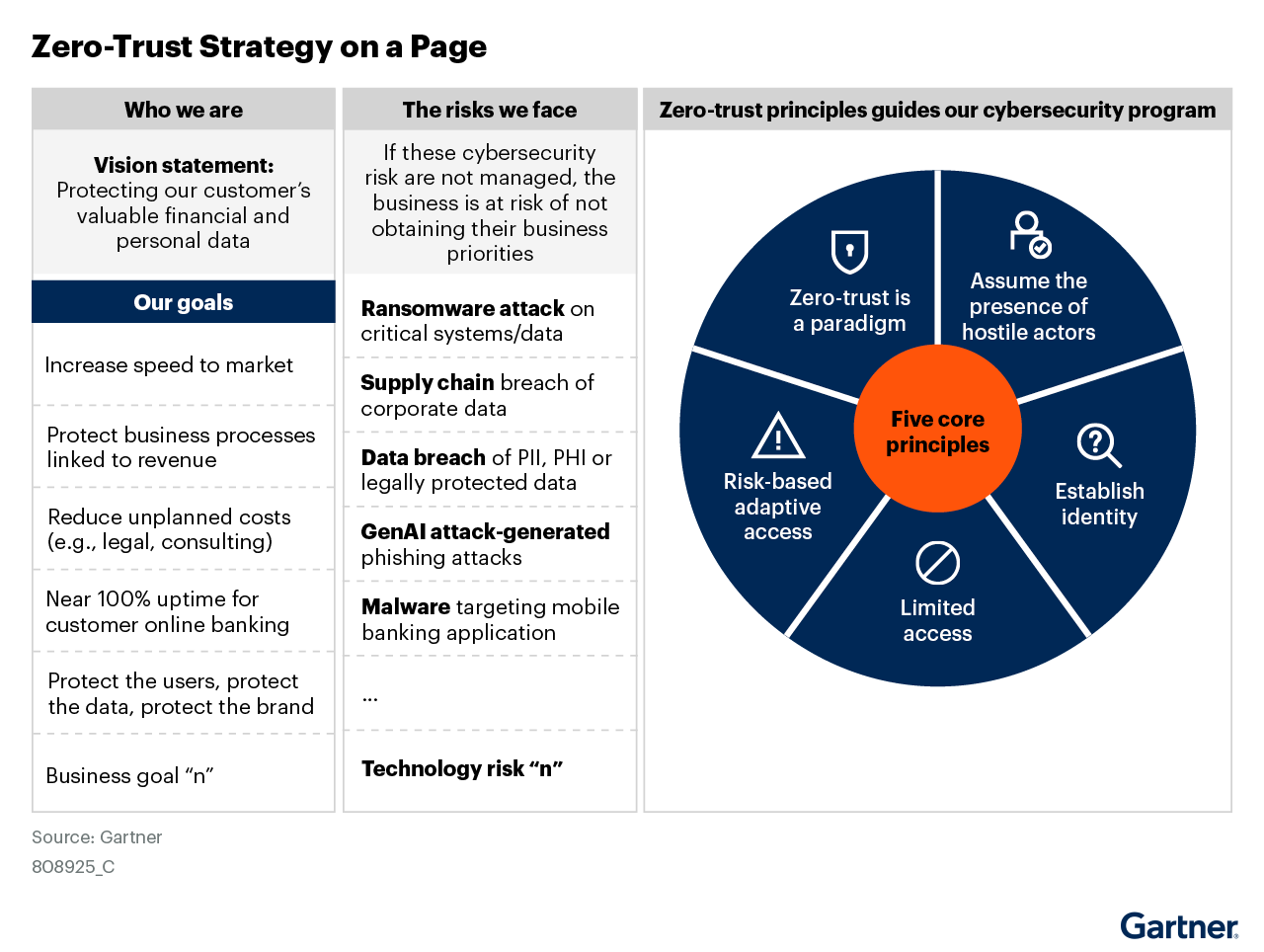
The Gartner report helps enterprises create a vision, specific goals, and risks with visuals like the one below:
Figure 5: Zero-Trust Strategy on a Page

Gartner, Strategic Roadmap for Zero-Trust Security Program Implementation, By Dale Koeppen et. al, 27 March 2025. This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Aviatrix.
GARTNER is a registered trademark of Gartner, Inc. and/or its affiliates and is used herein with permission. All rights reserved.
By guiding organizations to focus on a specific vision and define both general and specific goals, the Gartner report helps you avoid the common pitfalls of vague planning that cause failed Zero Trust implementations.
Why Enterprises Need this Report
As noted above, cloud security risks are growing, escalating, and adapting. Enterprise networks become more complex as teams scale across clouds and locations. As IBM and Palo Alto networks discovered, organizations use an average of 83 different security solutions from 29 vendors. This tool sprawl creates a cost and management nightmare. Threat actors can leverage shadow AI and agentic AI for advanced attacks like spear phishing, prompt injection, and supply chain manipulation.
Zero Trust is the most effective cloud security methodology because it makes security built-in, proactive, enforceable, and continuous. However, a stalled Zero Trust implementation wastes resources and may leave an enterprise’s security in a worst place than it was before. Use Gartner® Strategic Roadmap for Zero-Trust Security Program Implementation to launch a Zero Trust program that will give you invaluable agility, flexibility, and scalability.
Download the report to learn how to start or restart your Zero Trust implementation.
Gartner, Strategic Roadmap for Zero-Trust Security Program Implementation, By Dale Koeppen et. al, 27 March 2025
GARTNER is a trademark of Gartner, Inc. and/or its affiliates.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Aviatrix.